Introduction
Docker can be an efficient way to run web applications in production, but you may want to run multiple applications on the same Docker host. In this situation, you’ll need to set up a reverse proxy. This is because you only want to expose ports 80 and 443 to the rest of the world.
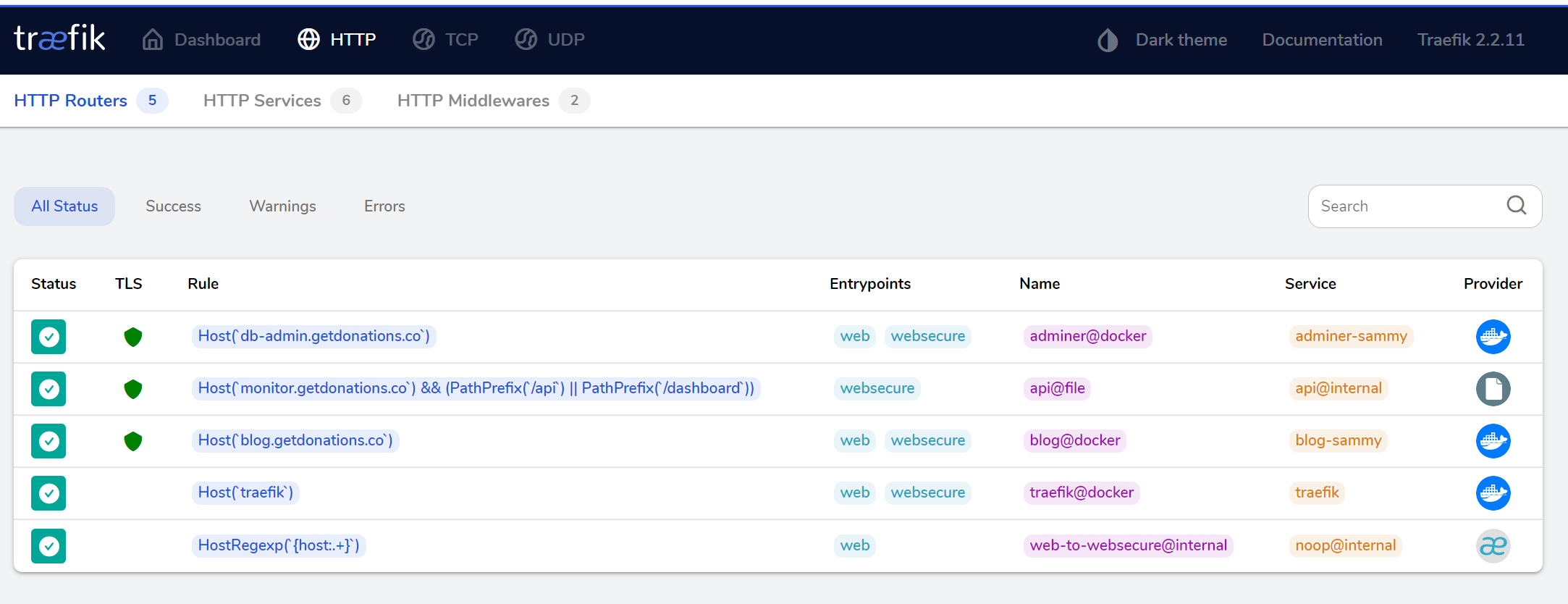
Traefik is a Docker-aware reverse proxy that includes a monitoring dashboard. Traefik v1 has been widely used for a while, and you can follow this earlier tutorial to install Traefik v1). But in this tutorial, you’ll install and configure Traefik v2, which includes quite a few differences.
The biggest difference between Traefik v1 and v2 is that frontends and backends were removed and their combined functionality spread out across routers, middlewares, and services. Previously a backend did the job of making modifications to requests and getting that request to whatever was supposed to handle it. Traefik v2 provides more separation of concerns by introducing middlewares that can modify requests before sending them to a service. Middlewares make it easier to specify a single modification step that might be used by a lot of different routes so that they can be reused (such as HTTP Basic Auth, which you’ll see later). A router can also use many different middlewares.
In this tutorial you’ll configure Traefik v2 to route requests to two different web application containers: a WordPress container and an Adminer container, each talking to a MySQL database. You’ll configure Traefik to serve everything over HTTPS using Let’s Encrypt.
Prerequisites
To complete this tutorial, you will need the following:
-
-
- One Ubuntu 20.04 server with a sudo non-root user and a firewall. You can set this up by following your Ubuntu 20.04 initial server setup guide.
- Docker installed on your server, which you can accomplish by following Steps 1 and 2 of How to Install and Use Docker on Ubuntu 20.04.
- Docker Compose installed using the instructions from Step 1 of How to Install Docker Compose on Ubuntu 20.04.
- A domain and three A records,
db-admin.your_domain,blog.your_domainandmonitor.your_domain. Each should point to the IP address of your server. You can learn how to point domains to DigitalOcean Droplets by reading through DigitalOcean’s Domains and DNS documentation. Throughout this tutorial, substitute your domain foryour_domainin the configuration files and examples.
Step 1 — Configuring and Running Traefik
The Traefik project has an official Docker image, so you will use that to run Traefik in a Docker container.
But before you get your Traefik container up and running, you need to create a configuration file and set up an encrypted password so you can access the monitoring dashboard.
You’ll use the
htpasswdutility to create this encrypted password. First, install the utility, which is included in theapache2-utilspackage:$ sudo apt-get install apache2-utils
The output from the program will look like this:
Outputadmin:$apr1$ruca84Hq$mbjdMZBAG.KWn7vfN/SNK/Youu’ll use this output in the Traefik configuration file to set up HTTP Basic Authentication for the Traefik health check and monitoring dashboard. Copy the entire output line so you can paste it later.
To configure the Traefik server, you’ll create two new configuration files called traefik.toml and traefik_dynamic.toml using the TOML format. TOML is a configuration language similar to INI files, but standardized. These files let us configure the Traefik server and various integrations, or providers, that you want to use. In this tutorial, you will use three of Traefik’s available providers: api, docker, and acme. The last of these, acme, supports TLS certificates using Let’s Encrypt.
Create and open traefik.toml using nano or your preferred text editor:
$ nano traefik.toml
First, you want to specify the ports that Traefik should listen on using the entryPoints section of your config file. You want two because you want to listen on port 80 and 443. Let’s call these web (port 80) and websecure (port 443).
Add the following configurations:>
traefik.toml
Note that you are also automatically redirecting traffic to be handled over TLS.
Next, configure the Traefik api, which gives you access to both the API and your dashboard interface. The heading of [api] is all that you need because the dashboard is then enabled by default, but you’ll be explicit for the time being.
Add the following code:
traefik.tomlTo finish securing your web requests you want to use Let’s Encrypt to generate valid TLS certificates. Traefik v2 supports Let’s Encrypt out of the box and you can configure it by creating a certificates resolver of the type
acme.Let’s configure your certificates resolver now using the name
lets-encrypt:traefik.tomlThis section is called
acmebecause ACME is the name of the protocol used to communicate with Let’s Encrypt to manage certificates. The Let’s Encrypt service requires registration with a valid email address, so to have Traefik generate certificates for your hosts, set theemailkey to your email address. You then specify that you will store the information that you will receive from Let’s Encrypt in a JSON file calledacme.json.The
acme.tlsChallengesection allows us to specify how Let’s Encrypt can verify that the certificate. You’re configuring it to serve a file as part of the challenge over port443.Finally, you need to configure Traefik to work with Docker.
Add the following configurations:
traefik.tomlThe
dockerprovider enables Traefik to act as a proxy in front of Docker containers. You’ve configured the provider towatchfor new containers on thewebnetwork, which you’ll create soon.Our final configuration uses the
fileprovider. With Traefik v2, static and dynamic configurations can’t be mixed and matched. To get around this, you will usetraefik.tomlto define your static configurations and then keep your dynamic configurations in another file, which you will calltraefik_dynamic.toml. Here you are using thefileprovider to tell Traefik that it should read in dynamic configurations from a different file.Add the following
fileprovider:traefik.toml -